On 20 April 2026, at Hannover Messe, STACKIT announced ES³ (the European Sovereign Stack Standard) with a headline that went straight for the jugular of every vague sovereignty claim in the market: “Ending Sovereignty Washing: STACKIT Makes Digital Sovereignty Objectively Measurable with ES³."
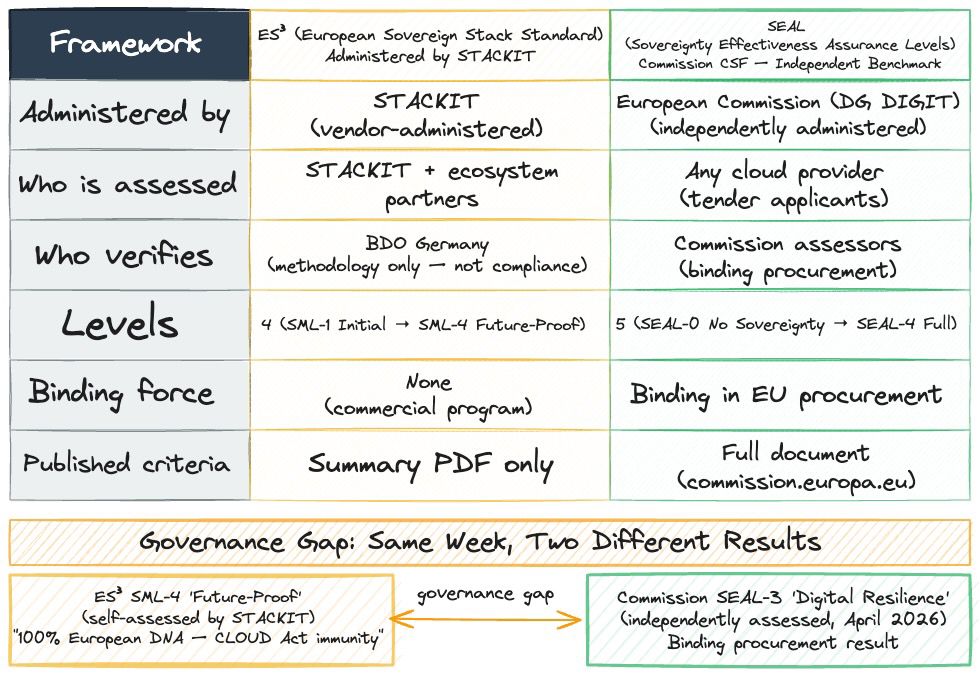
Three days earlier, on 17 April, the European Commission had published the results of its own sovereign cloud tender: a binding procurement assessment using its CSF (Cloud Sovereignty Framework), the same framework ES³ claims as its foundation. The CSF scores providers on the SEAL scale (Sovereignty Effectiveness Assurance Levels), running from SEAL-0 (no sovereignty) to SEAL-4 (full digital sovereignty). The Commission’s independent assessment placed STACKIT at SEAL-3 (Digital Resilience). Not SEAL-4. Not ES³’s “Future-Proof” top tier.
The gap between those two statements is what this article is about.
STACKIT: Context First
STACKIT is operated by Schwarz Digits Cloud GmbH & Co. KG, headquartered in Neckarsulm, Germany. It’s the cloud arm of Schwarz Group, the retail conglomerate behind Lidl and Kaufland, which employs 595,000 people across 32 countries. STACKIT was launched in 2018 to serve the Group’s own digital infrastructure needs and has since grown into a commercial cloud provider with data centers in Germany (Neckarsulm, Ellhofen, and a site in Lübbenau under construction) and Austria (Ostermiething).
The timing of the ES³ launch and the Commission tender result (three days apart) isn’t coincidental. STACKIT is in a moment. On 17 April, the Commission named it as one of four providers awarded contracts under a €180 million, six-year sovereign cloud tender. On 23 April, the Dutch government signed a framework agreement via SLM Rijk (the Dutch government’s Strategic Supplier Management body) covering Dutch central-government organisations on voluntary terms (approximately 1,400 institutions per Techzine’s reporting on SLM Rijk’s procurement scope). Dutch State Secretary Willemijn Aerdts, responsible for Digital Economy and Sovereignty, framed the deal pragmatically: “Digital autonomy means having the freedom to choose from a wide range of providers, ensuring competition and innovation.”
That framing (expanding options, not declaring sovereignty solved) is more honest than some of what STACKIT’s own marketing implies.
What ES³ Actually Measures
ES³ uses a Sovereignty Maturity Level (SML) framework across nine dimensions. Eight of those dimensions map directly to the Commission’s CSF (SOV-1 through SOV-8, covering strategic sovereignty, legal and jurisdictional, data and AI, operational, supply chain, technology, security, and environmental sustainability). STACKIT added a ninth: an explicit AI governance dimension. The assessment runs at three levels within each dimension: regulatory (contractual), organizational (process), and technology (technical).
The SML levels run from Level 1 (Initial) through Level 4 (Future-Proof). A minimum principle applies: your overall SML score equals your lowest dimension score, regardless of how well you perform everywhere else. That design choice is architecturally sound. It mirrors the same minimum principle the Commission uses in SEAL scoring.
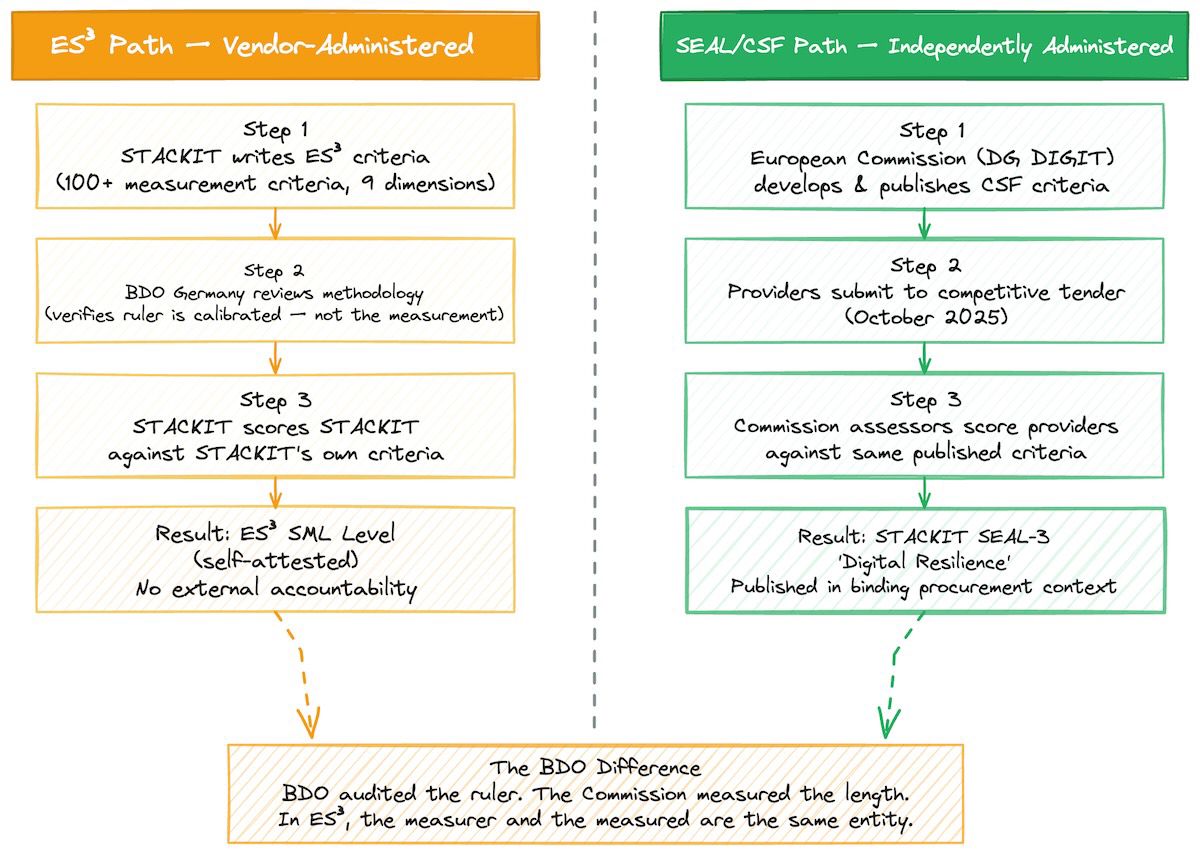
STACKIT claims ES³ contains over 100 measurement criteria. The framework methodology was verified by BDO Germany, one of the major German audit and advisory firms.
That last sentence is doing more work than it looks like.
The BDO Question
BDO Germany verified the framework. That means they audited ES³’s methodology for internal consistency and completeness: whether the 100+ criteria hold together as a measurement system. What BDO did not do is audit STACKIT’s own compliance against those criteria.
This is a structurally different claim from what the press release implies.
In standard compliance contexts, “independently verified” typically means an independent auditor assessed the subject against defined criteria and found them compliant. What STACKIT has is closer to: an auditor confirmed that the ruler is correctly calibrated, not that the thing being measured is the right length. The entity writing the criteria and the entity being scored against those criteria are the same entity. BDO’s role was to verify the methodology, not to hold STACKIT accountable to it.
STACKIT’s own documentation hedges this correctly (“the objective criteria of the SML framework are verified by the independent auditing body BDO”) but the press release headline does not. “Objectively measurable” is a statement about the framework’s design. It says nothing about who holds the measuring tape.
Compare that to the Commission’s CSF. The SEAL assessment of STACKIT was conducted by the procuring institution itself, using published criteria available at the Commission’s document repository, in a competitive tender context where four providers were measured against the same criteria by the same assessors. That is a different trust model.
What the Commission Actually Found
The Commission’s April 2026 tender placed STACKIT at SEAL-3, alongside Scaleway (the French cloud provider part of Iliad Group) and Post Telecom (Luxembourg) with OVHcloud and CleverCloud. Proximus (Belgium) with its S3NS partnership (S3NS is the sovereign cloud joint venture between Thales and Google, operating under French law) reached SEAL-2, the minimum eligibility threshold for public procurement under the CSF.
SEAL-3 is the “Digital Resilience” tier in the Commission’s framework. The Commission defines it as services, technology, or operations that are immune from supply-chain disruption from non-EU third parties. In practice that requires EU operational control as well, which the framework picks up under the operational-sovereignty objective (SOV-4). It’s a strong result. STACKIT holds it for structural reasons: German legal entity, EU-only data centers, BSI C5 Type 2 certification (BSI is the German Federal Office for Information Security; C5 is its Cloud Computing Compliance Criteria Catalogue) covering approximately 20 products including Compute Engine, Object Storage, and Kubernetes Engine.
What SEAL-3 is not is SEAL-4. The Commission’s SEAL-4 requires complete EU supply-chain independence from chips to software, zero third-country dependency in the critical path. The Commission assessed STACKIT at SEAL-3. Yet ES³’s SML-4 “Future-Proof” level claims “100% European DNA” and “immunity against external interference such as the U.S. CLOUD Act.”
If STACKIT’s own top tier requires 100% European DNA, and the Commission’s independent assessment placed STACKIT one rung below that ceiling, something in the self-assessment math doesn’t close.
One supply-chain detail is worth naming specifically: ServiceNow (a US company) appears in STACKIT’s BSI C5-certified product scope. C5 certification covers STACKIT’s service delivery on top of ServiceNow, not ServiceNow itself. For teams doing SOV-5 (Supply Chain) analysis at SEAL-4 resolution, that’s the kind of detail that matters. The Commission apparently agrees, given its SEAL-3 result.
The full per-objective scores from the Commission’s tender assessment were not published in the press release, and the granular SOV-N breakdown for STACKIT was not available in the research conducted for this article. What is confirmed, from the Commission’s primary source, is the overall SEAL-3 designation.
Three Sovereignty-Washing Patterns Worth Naming
The ES³ launch press release and STACKIT’s broader marketing contain three patterns that deserve some scrutiny before they show up in a procurement pitch deck.
Pattern 1: Residency as sovereignty. STACKIT correctly notes that its infrastructure runs in Germany and Austria. Data stays in the EU. That’s data residency. It’s a real and important property. But it’s not the same as legal sovereignty. Germany is subject to German law (including §§ 113 TKG and BKAG, the German telecommunications and criminal procedure codes that allow government data access under defined legal procedures). No EU-domiciled company has legal immunity from its own government. The claim that the “legal attack surface remains at zero” appears in STACKIT’s company boilerplate. It is not operationally accurate. It implies a level of legal immunity that no EU-domiciled company actually has, including STACKIT. The distinction matters: STACKIT’s legal exposure is governed by EU and German law (not the US CLOUD Act, which is a genuine advantage over US-headquartered providers), but that’s not the same as zero.
Pattern 2: Framework lineage. STACKIT’s press release describes ES³ as making sovereignty “measurable for the first time.” The Commission’s CSF, which ES³ explicitly builds on, was used in a procurement tender launched in October 2025, six months before the ES³ launch at Hannover Messe. The Commission built the measurement tool first. STACKIT adapted it, added an AI dimension, and built a commercial ecosystem program around it (an “ES³ Lens” presales tool, an SML seal, a partner network). That’s valuable product work. But the “first time” framing in the press release actively obscures the lineage. The canonical independent framework predates the proprietary one.
Pattern 3: Measuring yourself. ES³ is a STACKIT program. There is no independent governance body, no public consultation process, and no evidence that ES³ has been submitted to any EU standardisation body such as ETSI (the European Telecommunications Standards Institute), CEN (the European Committee for Standardization), or ENISA (the EU Agency for Cybersecurity). The framework is administered by the entity being assessed, for the entity being assessed (and, eventually, for ecosystem partners who apply through STACKIT’s program). That’s not a failing specific to STACKIT. Many vendor security programs work this way. But using the word “objective” to describe a self-graded system, in a press release titled “Ending Sovereignty Washing,” invites exactly this kind of scrutiny.
What This Means for a Procurement Team
If you’re evaluating STACKIT for a regulated EU workload, the Commission’s SEAL-3 assessment is the most valuable signal available. It’s the result that matters for DORA (the Digital Operational Resilience Act, the EU regulation governing ICT risk management for financial services, in application since January 2025), NIS2 (the Network and Information Systems Directive, governing cybersecurity obligations for critical infrastructure and large enterprises) compliance conversations, and any procurement process that asks “what level of sovereignty can you demonstrate?”
SEAL-3 is a strong result. For most regulated EU financial services workloads, it’s sufficient. OVHcloud, Scaleway, and STACKIT all landed at SEAL-3 in the same Commission tender. The relevant architecture decisions at this level are about service maturity, operational tooling, and migration cost. Not about whether STACKIT is “sovereign.” It is, at SEAL-3.
ES³ is secondary evidence. It tells you how STACKIT has structured its internal measurement practice, and the minimum principle design is genuinely sound. But for external accountability, you want the Commission assessment, not the vendor’s own score.
Here’s a short checklist for when a vendor presents a self-graded sovereignty framework in a procurement context:
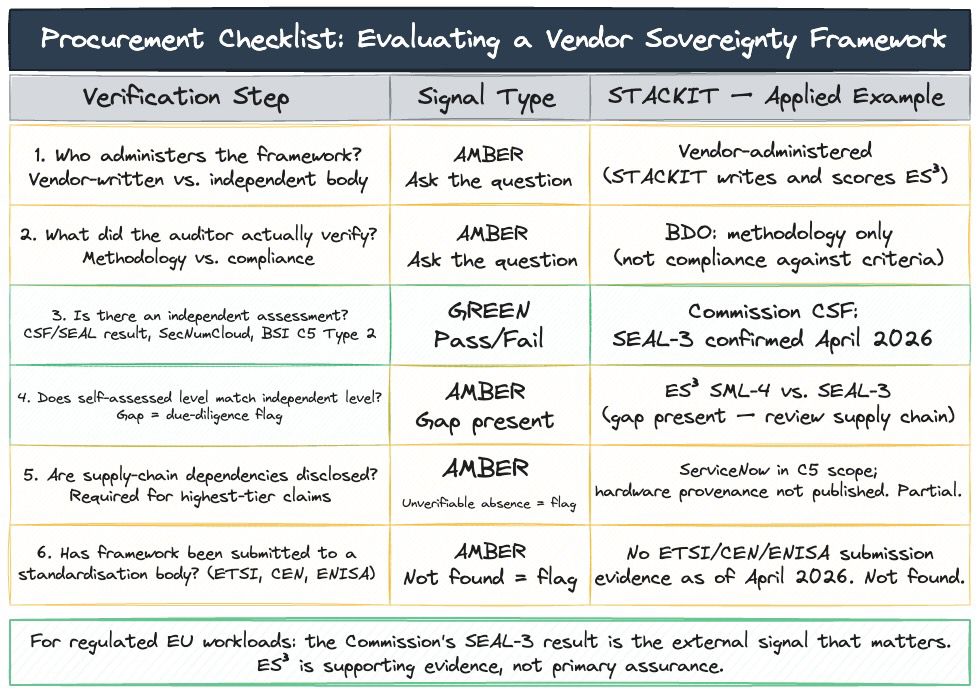
- Who administers the framework? If the vendor wrote the criteria and scores their own compliance, treat it as useful internal evidence, not external assurance.
- What did the auditor actually verify? Framework methodology and vendor compliance are different things. Ask for the audit scope statement.
- Is there an independent assessment? For EU sovereign cloud procurement, the Commission’s CSF result is the independent signal. SecNumCloud (administered by ANSSI, the Agence nationale de la sécurité des systèmes d’information, France’s national cybersecurity authority) is France’s national sovereign-cloud certification, with criteria that overlap heavily with SEAL-3 but are scoped to French law rather than the Commission’s framework.
- Does the self-assessed level match the independent level? A gap between what the vendor claims under its own framework and what an independent body assessed is a due-diligence flag, not disqualifying, but worth resolving.
- Are supply-chain dependencies disclosed? SEAL-4 and ES³ SML-4 both require complete EU supply-chain independence. If a vendor claims that tier but doesn’t disclose hardware provenance, the claim is unverifiable by design.
- Has the framework been submitted to a standardisation body? An ES³ submitted to ETSI or ENISA is a different thing from an ES³ that lives only as a proprietary STACKIT program. That submission has not happened as of April 2026, as far as available evidence shows.
The Dutch deal is worth examining through this lens. The Dutch government’s framework agreement, signed 23 April 2026, is a SEAL-2 instrument in practice: it’s a contract-level protection (including an exit clause if STACKIT comes under control of a non-EEA party) for a SEAL-3-assessed provider. The procurement rationale was explicitly about diversification: reducing reliance on US hyperscalers following concerns raised by situations like the Solvinity/Kyndryl acquisition, where an independent Dutch identity infrastructure provider fell under US corporate control. State Secretary Aerdts’s statement on the deal doesn’t claim full sovereignty. It claims optionality. That’s the politically honest framing.
Sovereignty assessments are only as useful as the independence of the assessor. ES³ is a well-designed internal measurement framework. The minimum principle, applied consistently across nine dimensions, is a genuinely useful tool for teams evaluating their own posture. The Commission’s SEAL framework does the same thing, administered by an institution with no commercial interest in the outcome.
The Commission put STACKIT at SEAL-3. STACKIT’s own ES³ framework, which STACKIT administers, implies a path to SML-4. Those two facts can coexist. But only one of them should drive your architecture decisions.
The assessor isn’t the assessed. That’s not a STACKIT problem. It’s the only question worth asking about any sovereignty framework.
This article describes STACKIT’s publicly available documentation and the European Commission’s published tender results as of April 2026. It is not legal advice. Specific compliance obligations depend on your entity type, jurisdiction, and regulator. Consult qualified legal counsel before relying on sovereignty assessments for architectural or procurement decisions.
