On 23 April 2026, the Plateforme des données de santé (Health Data Hub, or HDH), the public-interest group (groupement d’intérêt public, GIP) that operates France’s national health data platform, announced it had selected Scaleway as the future host of the Système national des données de santé (SNDS). For anyone who has been keeping score, this was always going to happen. It just took six years, two Conseil d’État rulings, four migration studies, one Senate “fiasco” report, an entire act of Parliament, and roughly €10.547 million in payments to Microsoft from 2019 to February 2026 to get there. The good news™: the migration is finally moving. The less good news: most of that delay was avoidable, and the architectural lesson worth extracting has very little to do with Microsoft, Scaleway, or anyone’s preferred flag.
The lesson is this. France took six years and a law to do what a reversibility-designed architecture enabled in one tender. Once you build cloud-agnostic from day one, sovereignty stops being a migration crisis and becomes a procurement decision. That distinction is the whole article.
How we got here, in roughly chronological order
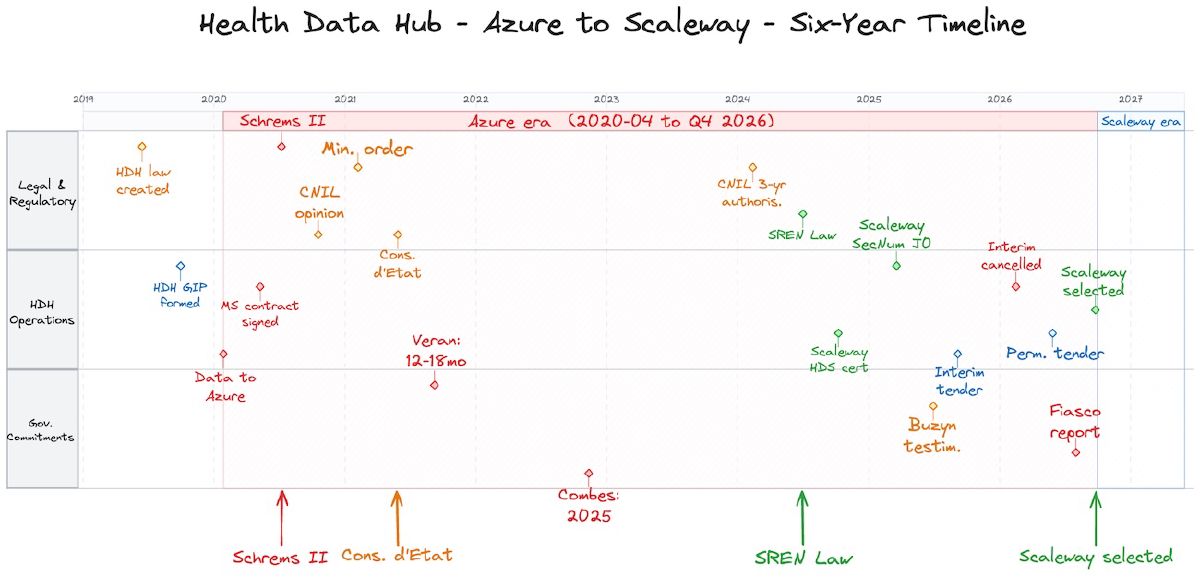
The HDH was created by Loi n° 2019-774 of 24 July 2019 (Article 41) and incorporated as a GIP in December 2019. Its job is to host the SNDS, France’s largest health administrative database, covering effectively every French resident’s interaction with the Assurance maladie. This is GDPR Article 9 special-category data: not “sensitive-ish” data, but the explicit category that triggers a stricter lawful-basis regime, sharper supervisory scrutiny, and now, since 2024, an explicit French legislative steer toward SecNumCloud-qualified hosting.
Hosting was awarded to Microsoft Azure, procured through the Union des groupements d’achats publics (UGAP) central purchasing catalogue, without a European public call for tenders. Capgemini ran a benchmark of technical solutions in 2018 before the prefiguration mission was even formally launched. Data started transferring to Azure on 10 April 2020, two months before the Microsoft contract was actually signed on 12 June 2020. The data lived in Microsoft Ireland Ltd’s Netherlands data centres, not in France.
Then the legal layer caught up.
The Court of Justice of the European Union (CJEU) handed down Schrems II (Case C-311/18) on 16 July 2020, invalidating the EU-US Privacy Shield and finding that the US Foreign Intelligence Surveillance Act (FISA) Section 702 and Executive Order 12333 did not provide adequate protection or effective redress for EU data subjects. On 13 October 2020, the Conseil d’État, ruling as juge des référés in ordonnance n° 444937, found that the risk of US intelligence access to HDH data could not be excluded, declined to order suspension, and required Microsoft to reinforce its contractual data-protection guarantees pending “une solution pérenne.” The Commission nationale de l’informatique et des libertés (CNIL, France’s data protection authority) had issued an opinion five days earlier recommending migration to a European, SecNumCloud-qualified host. A ministerial order of 9 October 2020 prohibited any transfer of HDH data outside the EU.
After which the political layer promptly slowed down. Health Minister Olivier Véran promised in November 2020 that a sovereign solution would arrive within “12 to 18 months.” It did not. By 2022, HDH Director Stéphanie Combes was talking about “the 2025 horizon.” In June 2025, former Health Minister Agnès Buzyn told a Senate commission, under oath: “C’était Microsoft ou rien… On ne m’a donné aucun choix.” In March 2026, a parliamentary inquiry labelled the whole episode a “fiasco.” The structural unblocker arrived a year earlier in the form of the SREN Law (Loi n° 2024-449 of 21 May 2024, “Sécurité et régulation de l’espace numérique”), which steered sensitive public-sector data toward SecNumCloud-qualified providers and limits reliance on hosts subject to extraterritorial foreign law. This is the legal instrument that finally forced the migration onto a calendar.
A first interim (“intercalaire”) tender was launched in July 2025, then cancelled by the government on 5 February 2026 in favour of jumping directly to a permanent SecNumCloud-targeted contract. The permanent tender went out 9 February 2026 under the UGAP “Nuage public” framework, evaluated against 350 technical requirements by panels from the Direction interministérielle du numérique (DINUM), Inria, and the Ministry of Health. Production cut-over of the main SNDS copy to Scaleway is targeted between end of 2026 and early 2027.
The pattern hiding behind the headline: reversibility-by-design
The part that gets lost in the political drama is this. The HDH’s announcement on 23 April 2026 highlighted that the platform was designed with “réversibilité” (reversibility) from 2019, meaning a cloud-agnostic architecture intended to avoid a full rebuild on provider change. That design choice is what made the swap mechanically feasible. Without it, six years of political deadlock would have hardened into vendor lock-in, and the Senate inquiry would have ended up explaining why the migration was technically impossible rather than politically delayed.
The transferable pattern, for any team running regulated workloads, is straightforward enough to write on a sticky note. Build cloud-agnostic from day one, even when, especially when, you deploy on a US hyperscaler for short-term reasons. That means: open formats for storage (object storage with S3-compatible APIs, columnar formats like Parquet, OMOP-CDM or comparable open data models for health), Kubernetes-shaped compute, Terraform or OpenTofu infrastructure-as-code with provider-agnostic modules where possible, and a key management architecture where the customer holds the root of trust outside the provider’s control plane. None of this is exotic. It just has to be a design constraint at day zero, not a refactor at year five.
Defer that decision, and what you’re actually committing to is this: any future regulatory or legal shift will land as a multi-year, board-level migration crisis, rather than a procurement event. The HDH’s 2019 architects bought their successors a six-year option. The successors used it.
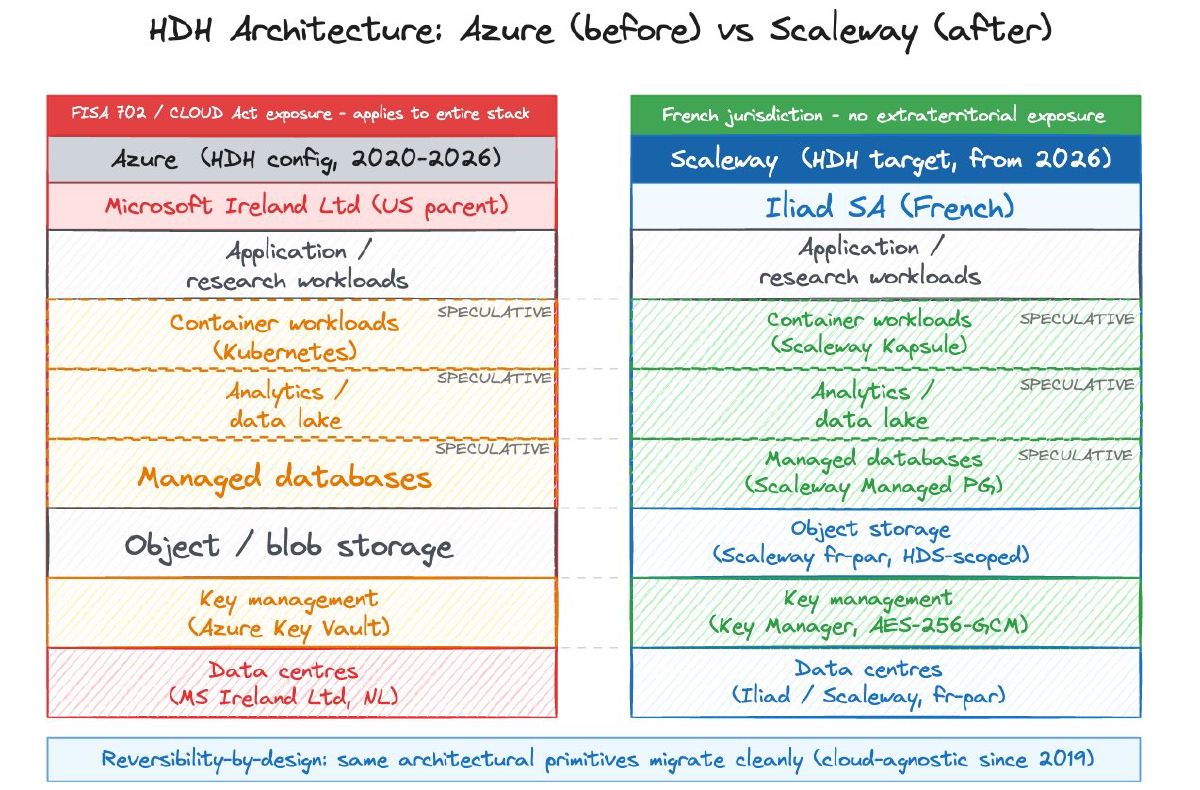
Architecture: before and after, with the honest caveats
The HDH has never published a detailed technical architecture for its Azure deployment, and the target Scaleway architecture is similarly unpublished. The mapping below uses the layers any large-scale health analytics platform tends to need, with cells flagged SPECULATIVE where the public record doesn’t confirm specifics.
| Layer | Azure (HDH config, 2020-2026) | Scaleway (HDH target, from 2026) |
|---|---|---|
| Primary data storage | Object/blob storage in Microsoft Ireland Netherlands DCs (confirmed location; specific service SPECULATIVE) | Scaleway Object Storage, fr-par region, HDS-scoped (confirmed scope; specific AZ SPECULATIVE) |
| Analytics / data lake | SPECULATIVE: standard Azure analytics stack | SPECULATIVE: not publicly disclosed |
| Container workloads | SPECULATIVE: managed Kubernetes | SPECULATIVE: Scaleway Kapsule (managed Kubernetes) |
| Managed databases | SPECULATIVE: managed PostgreSQL | SPECULATIVE: Scaleway Managed PostgreSQL |
| Key management | Azure Key Vault, with US-parent CLOUD Act exposure regardless of contractual no-transfer terms | Scaleway Key Manager: AES-256-GCM, root key in French-controlled HSM, not exportable, not visible to Scaleway employees |
| Data residency | Netherlands (Microsoft Ireland Ltd entity); ministerial order Oct 2020 prohibited extra-EU transfer | France only (fr-par); HDS scope explicitly limits to French DCs |
| Legal jurisdiction | US parent, FISA 702 and CLOUD Act structural exposure, EU-US Data Privacy Framework (DPF) provides partial mitigation but CNIL considers it insufficient for Article 9 data | Iliad SA (French), no US parent, no CLOUD Act / FISA 702 exposure |
| Reversibility design | Cloud-agnostic from 2019 | Maintained |
Specific Azure services and target Scaleway services are not in the public record as of 29 April 2026: the HDH has not published a deployment-level architecture for its Azure stack, and the HDH-Scaleway contract technical annex has not been released alongside the 23 April 2026 selection announcement.
A note on costs, because someone is going to ask. Microsoft was paid €10.547 million across the 2019-February 2026 window, with Capgemini paid roughly €10 million on the same project (per Next.ink reporting on parliamentary disclosures). The HDH-Scaleway contract financial terms have not been disclosed publicly: the 23 April 2026 announcement and follow-on coverage (Banque des Territoires, DSIH, Maddyness, Euronews, Solutions-Numériques) describe the UGAP “Nuage public” framework, the 350-criterion scoring grid, and the security/scalability/resilience selection logic, but no contract value has been published. So no, this article is not going to invent a saved-X-million headline. If you’re modelling for your own migration, model on like-for-like service costs, exit costs, and the cost of operational team retraining; do not assume a sovereign provider is cheaper just because someone wants the narrative.
A migration playbook, in four patterns
Read the HDH story as a single case study and you can extract four patterns that travel well to any regulated workload, public or private.
1. Reversibility-by-design. Already covered above, but worth repeating: cloud-agnostic primitives, open data formats, IaC that doesn’t bind you to a provider’s proprietary control plane, and explicit exit-cost line items in the operational budget. This is what turns a forced migration from an extinction-level event into a six-month roadmap item.
2. Procurement as a security control. The original Azure decision was made through a non-competitive UGAP catalogue route. The 2026 reprocurement, by contrast, ran 350 technical requirements through expert panels from DINUM, Inria, and the Ministry of Health, with security, scalability, and resilience as the three decisive criteria. For private-sector teams, the equivalent is your internal architecture review board: if the same workload would get rubber-stamped on procurement and stress-tested at architectural review, your procurement layer is doing the wrong job. Move sovereignty criteria into the procurement template, not into the architecture-review afterthought.
3. The certification cascade. Hébergeur de Données de Santé (HDS) is mandatory for any French health-data hosting; Scaleway holds it (since July 2024) and is transitioning to the v2.0 framework published 16 May 2024 with a deadline of 16 May 2026. SecNumCloud 3.2 is what the SREN Law steers toward and what the Agence nationale de la sécurité des systèmes d’information (ANSSI) qualifies. Scaleway entered the SecNumCloud 3.2 qualification process in January 2025, clearing the J0 milestone “without reservation,” and as of 29 April 2026 it remains on the ANSSI “prestataires en cours de qualification” list at cyber.gouv.fr (service: “Scaleway SecNumCloud (IaaS, PaaS)”) — i.e. in process, not yet qualified. The original “objectif fin 2025” target (per Scaleway and contemporaneous press) has slipped, which is consistent with the published 18-24 month J0-to-qualification window. SecNumCloud is not, by published rules, a prerequisite of the HDH tender; it was a “decisive argument.” Practitioners should expect this in any sovereign migration: layered, time-sequenced certifications, not a single binary stamp. Plan your roadmap against which certifications gate which decisions, and write that table down before you sign anything.
4. Key management as the legal break-point. The Conseil d’État ruling in 2020 was not really about data location. The data was in the Netherlands; that was not the problem. The problem was that legal access could be compelled through a US-parent operator’s chain of control, regardless of what the contract said. The architectural fix is cryptographic, not contractual: customer-held keys, root of trust outside the provider’s reach, hardware-security-module-backed key material that the provider cannot export or read. Scaleway’s Key Manager design (AES-256-GCM, root key non-exportable, not visible to employees) is structurally consistent with that pattern. A “we promise not to transfer” clause is not. If you’re running anything subject to GDPR Article 9 or DORA-style operational-resilience scrutiny, the question to ask your provider is not “where is the data” but “who can be lawfully compelled to decrypt it.”
A bonus pattern worth flagging because it bites people sideways: the EU-US Data Privacy Framework adopted on 10 July 2023 is the third iteration of EU-US transfer adequacy, after Safe Harbor (struck down 2015) and Privacy Shield (struck down 2020). The CNIL has consistently treated DPF as insufficient cover for Article 9 health data. Building long-term sovereignty strategy on DPF stability is a bet that the third try will be the one that holds, when the historical base rate is zero out of two.
Concrete scenario: a European fintech with biometric onboarding
That playbook lands differently when the workload isn’t a French national health database. Imagine a Dutch lending platform, regulated under GDPR and starting to feel the weight of DORA, that runs its biometric onboarding (face match, liveness check) on a US hyperscaler in an EU region. Biometric data is GDPR Article 9 special-category, the same legal regime as health data. The CLOUD Act and FISA 702 questions are identical. The fintech’s risk register, today, almost certainly notes “data residency: EU” and rates the row green. That row is wrong.
Apply the four patterns. Reversibility-by-design: are the biometric vectors stored in an open format, on object storage with S3-compatible APIs, accessible from anywhere with the right keys? Or are they tangled into a provider-proprietary face-match service with no extractable representation? Procurement-as-control: when the next provider review happens, are sovereignty and extraterritorial-jurisdiction questions in the scoring template, or buried in an annex no one weights? Certification cascade: is the provider HDS-equivalent for biometric data (probably not), is it ISO/IEC 27001 (probably yes), and is there a SecNumCloud-style or C5 path for the categories you care about? Key management: who can be lawfully compelled to decrypt the biometric vectors? If the answer is “a US-parent corporation,” you are one CJEU ruling away from a board-level migration project.
The fintech doesn’t have to migrate today. It has to make sure that, the day a regulator or a court forces the question, the answer is “we initiated a procurement,” not “we initiated a six-year political crisis.”
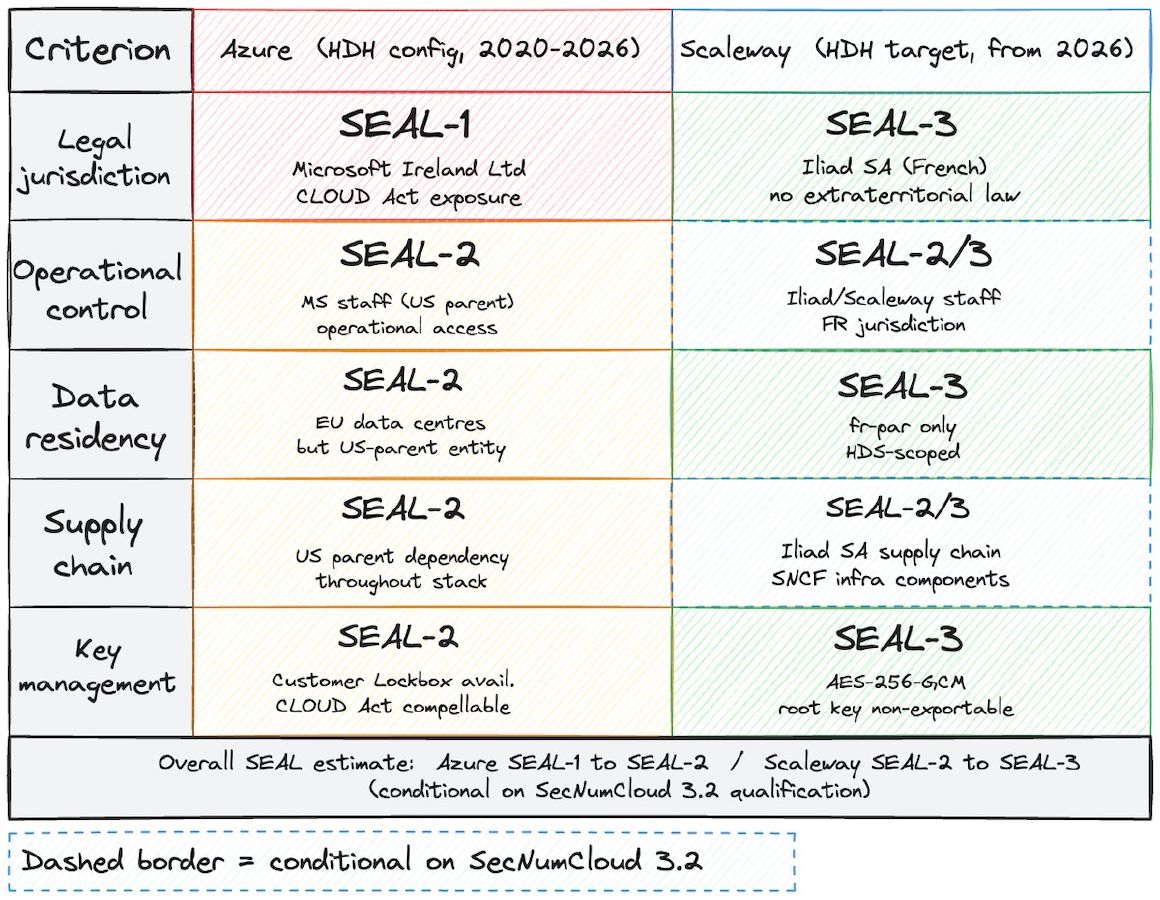
SEAL mapping
Mapping the HDH configurations to SEAL levels (the brand’s 5-criterion sovereignty assessment) gives a tractable picture of what actually changes between Azure and Scaleway for this specific workload. SEAL scores are interpretive judgments based on the public evidence; treat them as starting points for your own assessment, not as a compliance verdict.
The Azure HDH configuration sits at SEAL-1 to SEAL-2. EU data residency was contractually achieved (Netherlands DCs, ministerial extra-EU transfer ban). Legal jurisdiction is the structural ceiling: a US-parent operator under FISA 702 and the CLOUD Act cannot reach SEAL-3 for Article 9 health data, in the CNIL’s consistent reading, regardless of contractual reinforcements. The Conseil d’État explicitly described the configuration as awaiting “une solution pérenne.”
Scaleway in the HDH configuration targets SEAL-2 to SEAL-3, conditional. Data residency moves from Netherlands to France (HDS scope). Legal jurisdiction moves from a US parent to a French parent (Iliad SA, majority-controlled by Xavier Niel since the 2021 simplified public offer that took Iliad off the Paris stock exchange). Operational control moves under HDS-certified procedures. Key management moves to a structurally-isolated root-of-trust model. Full SEAL-3 defensibility, in my reading, lands when SecNumCloud 3.2 qualification is awarded and confirmed on the ANSSI public list. I’d treat the SecNumCloud qualification as a forward bet, not a present fact, and write the architecture-decision-record accordingly.
Next steps if you’re staring at a similar workload
A short, actionable checklist. Use it in this order; the order matters.
- Inventory your Article 9, biometric, financial, and any other special-category or sector-regulated data flows. Tag each one with current host, host’s parent jurisdiction, and current root-of-trust location.
- For every flow whose host has a non-EU parent, write the answer to “who can be lawfully compelled to produce or decrypt this data, and under which legal regime.” If the answer involves a foreign extraterritorial law, that flow is a sovereignty risk row, regardless of its data-residency label.
- Score each flow on the five SEAL criteria using public evidence. Flag the ceiling (which criterion caps your score) and what would have to change to lift it.
- Audit your stack for reversibility: open formats, S3-compatible storage, Kubernetes-shaped compute, IaC, customer-held key material. Note every place a proprietary primitive has been adopted for short-term convenience and what its exit cost is.
- Move sovereignty criteria into the procurement template before the next vendor review. Include extraterritorial-jurisdiction screening, certification cascade requirements, and key-management architecture as scored items, not as narrative annexes.
- For any workload likely to face a SecNumCloud-class requirement in the next 24 months, start scoping the migration roadmap now. Six years of advance notice was apparently not enough; do not bet on getting the same again.
The HDH took six years to do the obvious thing. Most teams reading this will not be afforded that runway. The good news™: the architectural pattern is portable, the certifications are documented, and the procurement playbook is now public record. The bad news: nobody is coming to write it for you.