On April 7, 2026, the European Commission tabled a new regulation to establish the EU Space Services Agency (EUSPA) as a standalone, permanent institution. This might not sound like a cloud decision, but it is. If your financial services organization relies on Galileo for navigation, Copernicus for earth observation data, or plans to use IRIS² for secure communications, space-based infrastructure is now a regulated SEAL-relevant factor.
The typical response in cloud architecture teams is: we don’t control satellites, so we don’t worry about them. That’s the wrong frame. Space infrastructure is infrastructure, like data centers, like DNS, like cloud APIs. When you build a dependency on it, you need to know what SEAL level it supports and where it fails.
What the EU Space Services Agency Actually Does
The new regulation COM(2026) 152 final amends Regulation (EU) 2021/696, which established the EU’s space programme for 2021-2027. The key change: EUSPA transitions from a time-limited, programme-focused agency to a permanent, standalone institution with expanded operational responsibilities.
Here’s why this matters for architecture. EUSPA currently operates two critical systems:
Galileo is the EU’s sovereign satellite navigation system. It’s fully operational with 26 satellites in active service and 2 more undergoing in-orbit commissioning (as of April 2026, per the European GNSS Service Centre). The default Open Service is accurate to within a few metres; the High Accuracy Service, which Galileo also broadcasts, gets you to sub-meter precision (horizontal error below 25 cm in Galileo-only mode). Unlike GPS (US-controlled) or GLONASS (Russian), Galileo operates under EU law and is managed by the Commission and operated by EUSPA. If you’re using Galileo for asset tracking, sanctions compliance verification, or supply chain visibility in financial services, you’re already dependent on EUSPA operations.
Copernicus provides free and open earth observation data covering land, oceans, and atmosphere. Financial services use this for climate risk assessment, ESG monitoring, regulatory reporting on environmental exposure, and geospatial verification of assets and sanctions targets. Again, fully operational.
But the new mandate goes further. EUSPA will now take responsibility for IRIS² (Infrastructure for Resilience, Interconnectivity and Security by Satellite), a roughly 290-satellite multi-orbit constellation designed to provide secure, sovereign EU communications. Initial GOVSATCOM Hub operations started in January 2026, pooling secure satellite capacity from five Member States (France, Greece, Italy, Luxembourg, and Spain) for EU governmental users. Cyprus completed the first operational use of the Hub in March 2026. The concession contract for IRIS² itself, with the SpaceRISE consortium (SES, Eutelsat, Hispasat), was signed in December 2024. As of early 2026, GOVSATCOM is operational but still scaling, with EUSPA describing ongoing preparatory activities and onboarding of government users. Full IRIS² operational capability is targeted for 2030.
The budget reflects the stakes. Current (2021-2027) allocation: 525.7 million euros. Proposed (2028-2034): 979.6 million euros.
Why This Changes Your Architecture
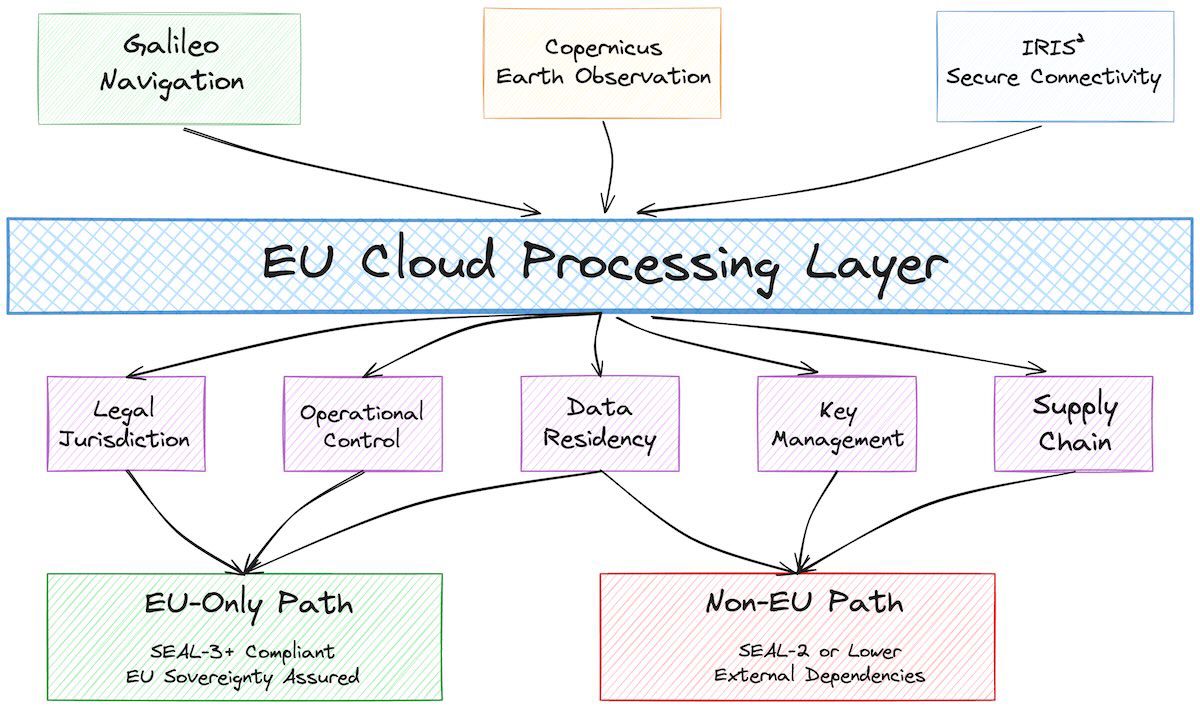
The SEAL framework assesses cloud services across eight sovereignty objectives: strategic, legal and jurisdictional, data and AI, operational, supply chain, security, environmental, and technological. Space-derived data and services fit squarely into SEAL criteria, specifically the supply chain and operational control objectives.
Consider a concrete case: a European insurance company using Copernicus earth observation data to assess flood risk for mortgage underwriting. The data is sourced from EU satellites, processed by EU infrastructure, and available under EU law. The data resides in the EU. But does the organization achieve SEAL-3 (digital resilience) by using it?
Not automatically. Here’s the gap. Copernicus data is free and open, which means you can’t technically control who accesses it or what they do with it. Your cloud architecture processes the data, but the SEAL-level assessment depends on three things: where the data came from (✓ EU), where it’s processed (your call), and how you contractually limit onward use.
If your cloud infrastructure processes Copernicus data and exports insights to a US-based parent company, you’ve created a SEAL-2 situation (data sovereignty, but with non-EU dependencies downstream). If you process it only within EU borders and restrict exports to verified SEAL-compliant counterparties, you approach SEAL-3.
The regulation itself doesn’t forbid either scenario. But the regulatory direction is clear: strategic space assets exist to support EU digital autonomy. Organizations relying on them should treat them seriously in SEAL assessments.
Three Patterns for Space-Data Handling in Financial Services
Most financial services organizations don’t need to operate their own satellites. But if you’re using satellite-derived data or services, you face three distinct patterns.
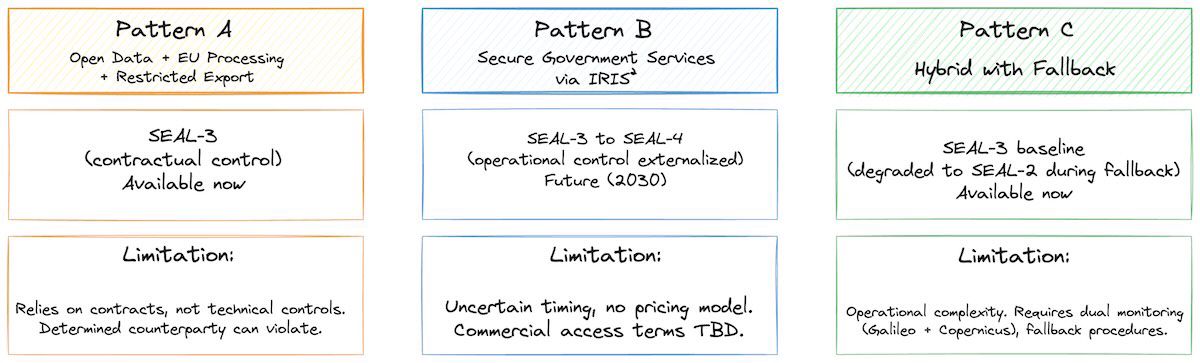
Pattern A: Open Data, EU Processing, Restricted Downstream Use
Use Copernicus earth observation data for internal risk assessment (climate exposure, asset verification, sanctions screening). Process the data on EU-based cloud infrastructure. Contract with downstream services and analysis tools to restrict their use of derived insights to EU-only distribution.
What it looks like: Copernicus data ingestion pipeline → internal risk models → restricted report export.
SEAL level: SEAL-3 (data sourced from EU, processed in EU, downstream restrictions contractually enforced).
When to use this: Organizations with primarily EU exposure. Risk that contractual restrictions are easier to define than technical controls. If downstream counterparties are mostly EU-based, this is tractable.
Limitation: You’re relying on contracts, not technical controls, to enforce restrictions. A determined counterparty can violate the contract. Verify that your EU data protection and export control counsel is comfortable with this model.
Pattern B: Secure Government Services via IRIS²
This is a future option, not available today. IRIS² government-grade secure communications (expected 2030) will be available to organizations that meet vetting requirements. These are likely to include financial services supporting critical infrastructure or cross-border payments.
What it looks like: Backup communications over IRIS² satellite network, EUSPA-managed key infrastructure, government-authorized encryption, EU ground stations.
SEAL level: SEAL-3 to SEAL-4 (if you qualify for government services, operational control is externalized to a vetted EU entity, key management is in EU hands).
When to use this: Organizations requiring high-availability critical communications and able to meet IRIS² accreditation requirements (security vetting, operational standards).
Limitation: Uncertain timing, unclear commercial access terms, no pricing model yet. IRIS² is currently positioned for government use (military, embassies, critical infrastructure). Whether commercial financial services get secondary access, and under what terms, is still being negotiated. Don’t plan on it before 2028.
Pattern C: Hybrid, with Fallback to Copernicus
Use Copernicus data as primary source for risk assessment, with Galileo as backup for time-critical location verification (sanctions compliance, real-time asset tracking). Process on EU cloud with documented SEAL-3 controls. Accept that during periods of system downtime or degradation, you may fall back to less-precise data or delayed processing.
What it looks like: Dual data sources, with predefined fallback thresholds.
SEAL level: SEAL-3 (baseline), degraded to SEAL-2 during fallback periods.
When to use this: Organizations that can tolerate graceful degradation. Regulatory compliance (sanctions screening, AML) can usually accept slightly delayed or lower-resolution data, as long as it’s documented.
Limitation: Operational complexity increases. You need to monitor system health for both Galileo and Copernicus, define fallback thresholds, and have manual override procedures. Automation reduces risk here, but adds development cost.
A Concrete Example: Fintech Lending Platform
An EU-based lending platform uses Copernicus data to assess climate risk for mortgage underwriting. Current setup: data ingested from Copernicus, processed on AWS eu-west-1, risk scores used in underwriting decisioning.
The SEAL assessment question: what level is this?
If the platform exports raw risk scores to a US-based parent company without restriction, it’s SEAL-2 (data sourced in EU, processed in EU, but downstream flows to non-EU entity with no contractual limits).
If the platform processes the data, derives risk scores, and keeps those scores internal to the EU entity (never exporting to parent), and the risk scores flow only into EU-jurisdiction lending decisions, the approach targets SEAL-3.
The regulation itself doesn’t block either approach. But future regulatory tightening (especially around AI in financial services and export controls on dual-use earth observation data) will likely move the needle toward SEAL-3 as the expected baseline for organizations claiming to be sovereignty-compliant.
Next Steps
Now (April 2026)
Audit your data dependencies. Do you use Galileo, Copernicus, or other space-derived services? Document them. For each dependency, identify: where the data originates, where it’s processed, and where derived insights flow.
Map dependencies to SEAL criteria. For Copernicus use: is your downstream distribution restricted to EU entities? For Galileo: is location data used only for internal compliance (sanctions, KYC), or is it exported?
By end of 2026
Review your export controls and data residency policies. If you’re using space-derived data, your data governance should explicitly address downstream use restrictions. This isn’t paranoid; it’s architecture.
Connect with your export control and data protection counsel. The IRIS² framework and dual-use export rules are still being finalized. Get ahead of changes.
2027-2028
Monitor IRIS² implementing acts. Once access terms and security requirements are published, evaluate whether government-grade secure communications fit your resilience requirements.
Plan for SEAL assessments that include space-derived data. This should be routine by 2028.
The EU’s strengthening of its space infrastructure isn’t about satellites. It’s about control. If your organization relies on data or services controlled by non-EU entities for critical decision-making, you’ve created a SEAL ceiling. Using sovereign EU space infrastructure is one of the few ways to improve that ceiling. The new regulation makes that explicit.
