I came across a stat that’s been nagging at me all week: 28% of EU organisations under NIS2 scope take more than three months to patch critical vulnerabilities on production systems. Not lab environments, not legacy systems nobody cares about. Critical vulnerabilities on production infrastructure. And this is after DORA went live in January 2025. That 28% covers all NIS2 sectors, not just financial services. But given the overlap between NIS2 and DORA scope, it’s a safe bet the finance sector isn’t immune.
Before you think “sure, maybe they’re understaffed,” here’s the thing. The median cybersecurity budget is €1.5 million. Nine percent of the entire IT budget goes to security. Seventy percent of organisations say regulatory compliance (NIS2 and DORA specifically) is driving these investment decisions. The money’s there. The patches aren’t moving.
That gap is worth understanding.
What the 2025 ENISA reports actually tell us
ENISA dropped three reports in 2025 that paint a pretty coherent picture if you read them together. None of it is dramatic. It’s just the kind of uncomfortable that makes you want to quietly check your own patch logs.
The threats aren’t hypothetical
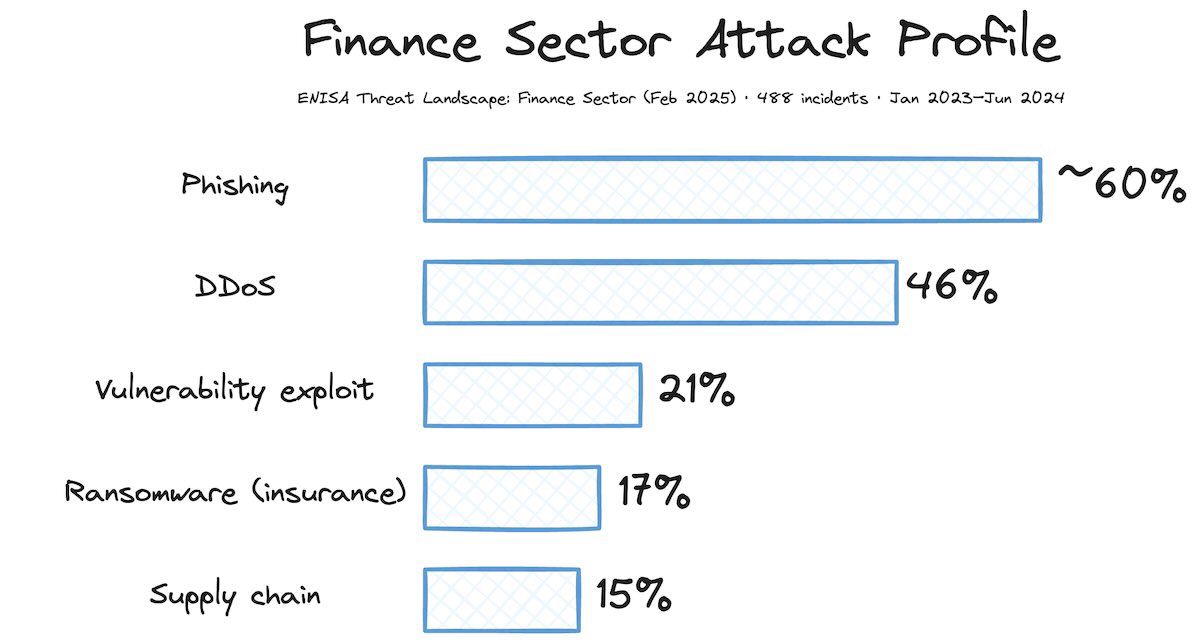
ENISA analysed 488 publicly reported incidents targeting European financial services between January 2023 and June 2024. Credit institutions accounted for 46% of them. The attack mix tells you what to architect for:
DDoS accounts for 46% of finance sector incidents, the single most common attack type. If you’re building cloud infrastructure for a financial institution, DDoS mitigation capability moves from “nice feature” to “selection criterion.” You need either cloud providers with serious absorptive capacity or dedicated scrubbing services positioned to handle the traffic before it hits your network. (For context, DDoS hits 77% across all sectors in ENISA’s broader 2025 Threat Landscape. Finance is lower, but it’s still the dominant threat.)
Phishing runs at roughly 60% of incidents, and here’s where it gets interesting: globally, 80% of observed phishing campaigns now use AI-powered social engineering. The attacks aren’t just more frequent, they’re sharper. An AI system can generate convincing impersonations at scale in ways a manual attacker simply can’t.
Supply chain attacks sit lower in the statistics but carry outsized impact. When attackers hit vendors or service providers, the consequences cascade. Sixty-three percent of cases led to data exposure. Twenty-six percent caused operational disruption. Eleven percent hit the bottom line directly. DORA’s third-party risk provisions exist because this pattern keeps repeating.
Ransomware hits service providers hardest (29% of cases), then insurance firms (17%). The damage splits across financial loss (38%), data exposure (35%), and operational disruption (20%). The diversity of impact is the point. It’s not one problem you can throw a tool at. It’s multiple failure modes hitting the same target from different angles.
The defences have real gaps
The ENISA NIS Investments 2025 report pulled data from 1,080 professionals across EU organisations (all NIS2-scope sectors, not just financial services). The findings hit close to home for anyone in finance:
30% haven’t done a cybersecurity assessment (a proper penetration test or audit) in the past 12 months. Under DORA’s ICT risk management framework, that’s not just a gap. That’s a finding you’ll be explaining to your regulator while they take notes.
50% say vulnerability and patch management is their top NIS2 challenge. Half the organisations under NIS2 scope are struggling with the most basic security hygiene. It’s not exotic threat prevention. It’s keeping track of what you need to fix and actually fixing it.
28% take over three months to patch critical vulnerabilities on critical systems. Three months is an eternity in the world of active exploits. Weaponised CVEs typically appear within days of public disclosure. If your patch window is 90 days, you’re operating with your guard down.
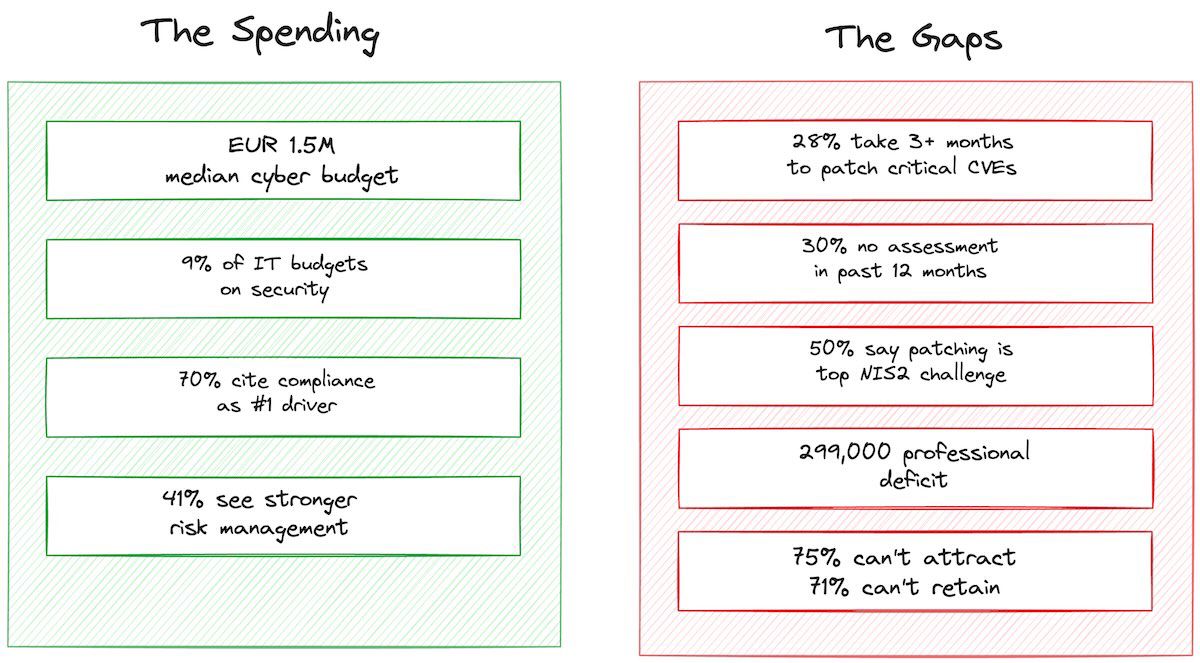
The talent problem is structural, not temporary
Here’s the constraint that makes everything harder: Europe has a shortage of 299,000 cybersecurity professionals. That’s not a cyclical dip you wait out. That’s structural. Seventy-six percent of organisations report trouble finding qualified staff. Seventy-one percent struggle to keep the people they hire.
The logical response is shift from people to platforms. Organisations across the EU are reallocating budgets away from headcount and into managed services. Most CTOs already know this intuitively, and ENISA’s data confirms it: you can’t hire your way out of a 299,000-person shortfall.
Where the data gets interesting
This is where ENISA’s cybersecurity findings meet the cloud sovereignty conversation, and where I think most discussion of these reports misses something important.
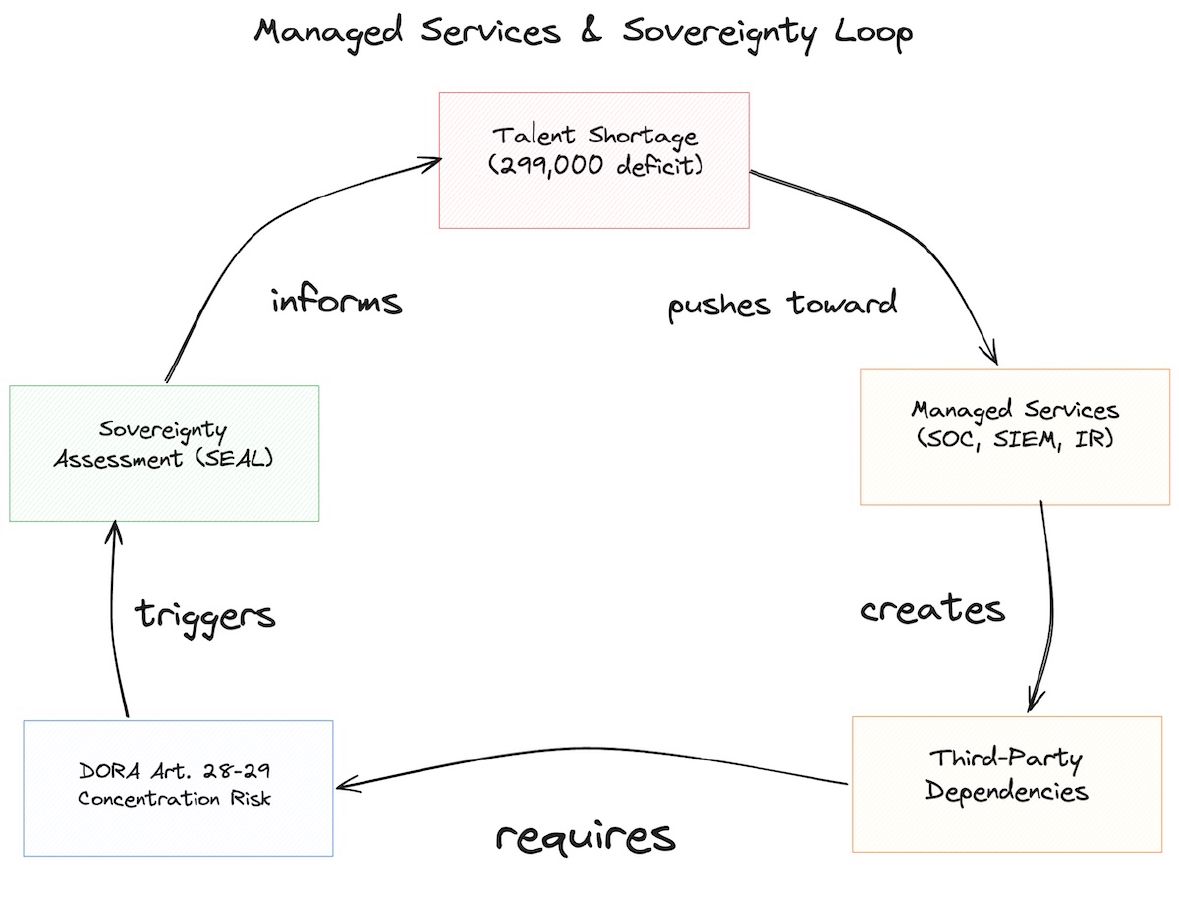
When you shift from in-house security teams to managed services (your SOC, threat intelligence, incident response platform, vulnerability scanning), you’re making a sovereignty decision whether you think about it or not.
Who runs your managed SOC? Which jurisdiction governs the service? If the provider is US-headquartered, what stops a US court order from compelling access to your incident data? We’re talking about data that might include customer personally identifiable information, transaction patterns, details of active vulnerabilities in your infrastructure. All the things you’d rather keep private.
DORA’s third-party risk provisions (Articles 28-30) and concentration risk rules (Article 29) exist because regulators thought through this exact scenario. The regulation asks three things: Is your provider secure? Are you dependent on them? Can you migrate away if things go wrong?
Here’s the loop. The talent shortage pushes you toward managed services. Managed services create third-party dependencies. Dependencies trigger DORA’s concentration risk checks. And if you haven’t sovereignty-assessed those managed services, you’ve traded one problem for another.
What I’d actually do with this data
If I’m sitting in a European financial institution reading these ENISA reports, here’s what lands as actionable.
1. Fix the patch problem first
If you’re in the 28%, this is your priority task. DORA expects “appropriate” response to vulnerabilities. Three months on a critical CVE won’t survive supervisory scrutiny.
Cloud-native infrastructure helps here. Managed Kubernetes, PaaS platforms, and infrastructure-as-code patterns all compress the time from “vulnerability disclosed” to “patch applied.” The trick is choosing the platform with sovereignty in view. Hyperscaler automation is fast. SecNumCloud-qualified provider automation is fast and sovereignty-compliant. Same speed, different risk profile.
2. Actually map your security supply chain
ENISA’s data on supply chain attacks (63% result in data exposure) should trigger one specific exercise: list every third-party service that touches your security operations. Managed SOC, SIEM platform, threat intelligence feeds, scanners, penetration testing retainers, incident response contracts.
For each one: who runs it, where, under which jurisdiction, what data do they access? This doubles as your DORA Article 28 register and your sovereignty assessment in one step.
3. Assess your managed services through the SEAL lens
The shift from people to platforms is rational. Lean into it. But think about the providers you’re adopting:
A managed SOC provider at SEAL-1 (US-headquartered, EU data centre, full access to your telemetry) and one at SEAL-3 (EU-headquartered, EU-operated, no non-EU exposure) are not the same thing. Not even close. The talent shortage isn’t going away. Your choice about how to respond to it is something you can control right now.
4. Make DDoS resilience a cloud selection criterion
When 46% of finance sector incidents are DDoS (more than any other single attack type), your provider’s DDoS mitigation capability stops being a feature and becomes a core evaluation criterion. Look at absorptive capacity, scrubbing centre locations, time-to-mitigate SLAs. And ask the hard question: does the DDoS architecture route traffic through non-EU points of presence?
Multi-provider architectures cut both DDoS risk and concentration risk. One architectural decision addresses two problems.
The bigger picture
ENISA’s banking sector maturity assessment notes that banking shows “high maturity in dealing with third-party risk” and “high spending efficiency” compared to other sectors. That’s a reasonable foundation. The frameworks and governance mostly exist. The challenge is applying them to managed services, cloud dependencies, and attacks that get smarter because they’re powered by AI now.
The data tells a story of an industry spending money, ticking compliance boxes, and still getting hit. The spending is necessary. It’s not sufficient. The compliance drives investment but doesn’t close basic gaps. And the talent shortage pushes everyone toward exactly the kind of third-party dependencies that DORA was designed to constrain.
This isn’t a doomsday read. It’s a signal about where to focus.
Every time you outsource a security function, you’re making a sovereignty decision.
ENISA’s reports show you where the threats actually are. DORA gives you the framework to manage dependencies. SEAL levels give you the language to assess providers.
The numbers don’t lie. The question is what you build with them.
This article is not legal advice. DORA compliance obligations vary by entity classification and jurisdiction. ENISA statistics are based on publicly reported incidents and may underrepresent actual attack volumes. Verify specific obligations with qualified counsel.
